Daemon * Freedom(TM)
Internet doomsday scenario
Every once in a while a science fiction book unleashes a vivid, important alternative vision of the future that has not been fleshed out before. Daniel Suarez does that with Daemon, a fasted-paced thriller about a world in which a virtual bot takes over. Sort of a digital Armageddon, only worse. It’s a techno-thriller more informed than a Tom Clancy novel, more plausible than The Matrix, more graphic than War Games, and more thought-provoking than Neuromancer — yet it introduces a science fiction future new to all of them. Here the ghostly bot upends the world by using technological blackmail to take control of more everyday infrastructural systems. Suarez, an information technology and security consultant in real life, makes this scenario entirely plausible even to a technology booster like myself. In fact his scenario is now being seriously considered by the intelligence and security agencies. In a stroke of genius, Suarez shows why this takeover by the bot might be something we choose to allow! The story is not a bit academic or abstract. Instead it is an action-packed made-for-Hollywood script. Warning: the ending is a cliff-hanger, concluded in the second book, Freedom(TM).
12/24/09Excerpt
Gragg's script also installed a keylogger, which gave him account and password information to virtually everything the user did from then on, sending it to yet another compromised workstation offshore where Gragg could pick it up at leisure.
What sort of idiot hung the keys to his business out on the street- and more than that, broadcast a declaration from his router telling the world where the keys were? These people shouldn't be left home alone, much less put in charge of peoples' investments. Gragg cleaned up the router's connection log. More than likely the scam wouldn't be detected for months, and even then, the company probably wouldn't tell their clients. They'd just close the barn door long after the Trojan horses were gone. So far, Gragg had a cache of nearly two thousand high-net- worth identities to sell on the global market, and the Brazilians and Filipinos were snapping up everything he offered.
*
But Decker was in no hurry. He finally placed his hand on a dis-connected rack server sitting on the nearby counter. "They tell me this computer killed two men earlier today." The shock took a while to work through Ross. He had expected some sort of child pornography ring, or a credit card scam.
"Killed? How?"
"I was hoping you could help us explain that."
*
Larson pointed to a network port in the side of the black box, then traced his finger to a smaller circuit board attached to it. "Check this out: it's a Web server on a chip. It's got a tiny TCP/IP stack. They're used for controlling devices like doors and lights from an IP network. I checked. They've got them all over the building." Larson slid his hand along a CAT5 cable extending from the board into the darkness. "This box is linked to their network, and their network is connected to the Internet. It's conceivable that someone with the right passwords could have activated this switch from anywhere in the world."
"Could the switch be set to activate when a certain person swiped their access card at the security door?"
"Probably. I just don't know enough about these cards yet."
"How long has the switch been here?"
Greer looked at the back of the enclosure. "It was covered in dust when we got to it."
"So that vestibule door has probably been used thousands of times without incident-then suddenly today it kills someone. ."
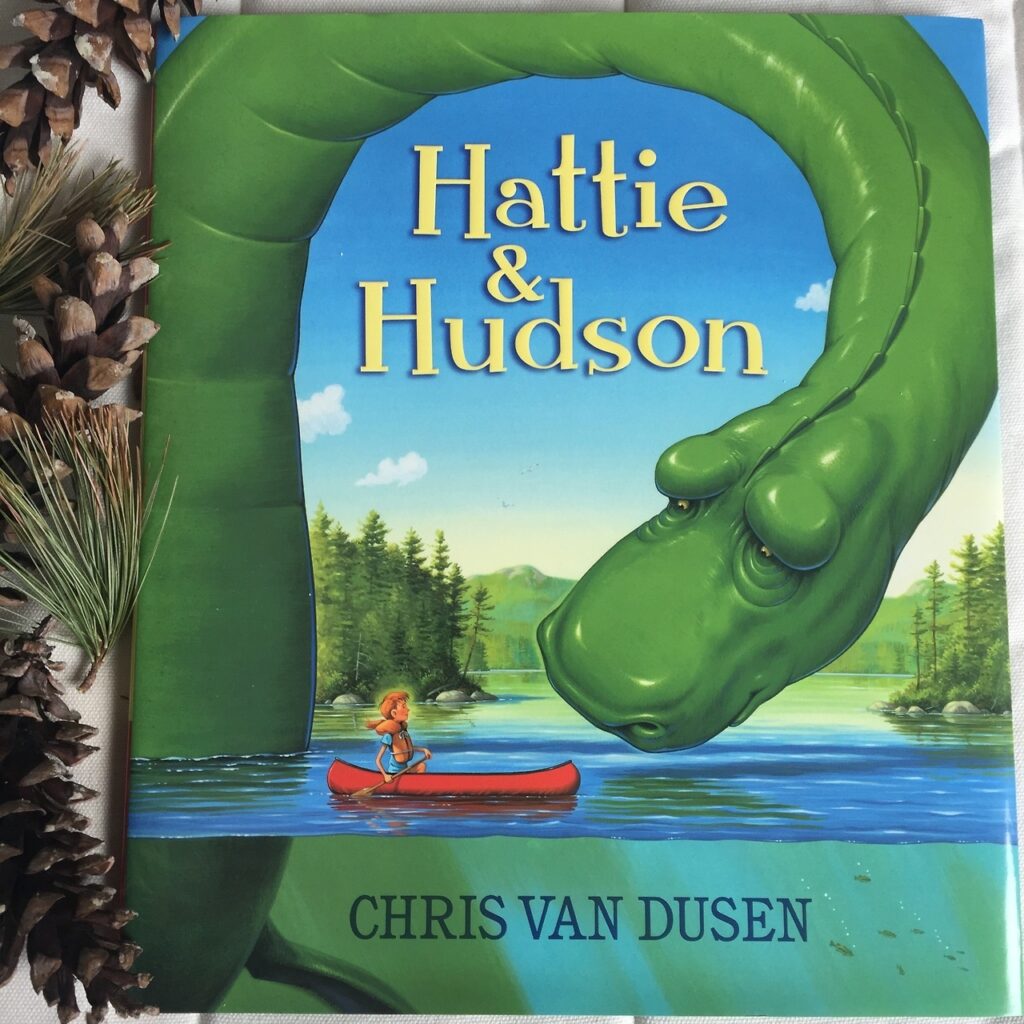
Daemon Daniel Suarez 2009, 640 pages $10 Available from Amazon Freedom(TM) Daniel Suarez 2010, 416 pages $18 Pre-order available from Amazon Book website