PLENTITUDE NOT SCARCITY
Value Flows from Abundance
Plentitude, not scarcity, governs the network economy. Duplication, replication, and copies run in excess. Whatever can be made, can be made in abundance. This plentitude:
- drives value
- works to open up closed systems
- spins off immense numbers of opportunities
Consider the first modern fax machine that rolled off the conveyor belt around 1965. Despite millions of dollars spent on its R&D, it was worth nothing. Zero. The second fax machine to be made immediately made the first one worth something. There was someone to fax to. Because fax machines are linked into a network, each additional fax machine that is shipped increases the value of all the fax machines operating before it.
This is called the fax effect. The fax effect dictates that plentitude generates value.
So strong is this power of plentitude that anyone purchasing a fax machine becomes an evangelist for the fax network. “Do you have a fax?” fax owners ask you. “You should get one.” Why? Because your purchase increases the worth of their machine. And once you join the network, you’ll begin to ask others, “Do you have a fax (or email, or Acrobat software, etc.)?” Each additional account you can persuade to join the network substantially increases the value of your account.
When you buy a fax machine, you are not merely buying a $200 box. Your $200 purchases the entire network of all other fax machines in the world and the connections among them–a value far greater than the cost of all the separate machines. Indeed, the first fax machines cost several thousands of dollars and connected to only a few other machines, and thus were not worth much. Today $200 will buy you a fax network worth $3 billion.
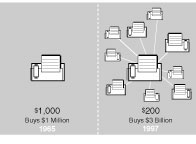
The low price of a fax machine today buys you an entire network, consisting of eighteen million machines. Each additional unit sold increases the value of your machine.
PLENTITUDE NOT SCARCITY
In the network economy, the more plentiful…
…things become, the more valuable they become.
This notion directly contradicts two of the most fundamental axioms we inherited from the industrial age.
First hoary axiom: Value comes from scarcity. Take the icons of wealth in the industrial age–diamonds, gold, oil, and college degrees. These were deemed precious because they were scarce.
Second hoary axiom: When things are made plentiful, they become devalued. For instance, carpets. They were once rare handmade items found only in houses of the rich. They ceased to be status symbols when they could be woven by the thousands on machines. The traditional law was fulfilled: commonness reduces value.
The logic of the network flips this industrial lesson upside down. In a network economy, value is derived from plentitude, just as a fax machine’s value increases as fax machines become ubiquitous. Power comes from abundance. Copies are cheap. Let them proliferate.
Ever since Gutenberg made the first commodity–cheaply duplicated words–we have realized that intangible things can easily be copied. This lowers the value per copy. What becomes valuable is the relationships–sparked by the copies–that tangle up in the network itself. The relationships rocket upward in value as the parts increase in number even slightly.
Windows NT, fax machines, TCP/IP, GIF images, RealAudio–all born deep in the network economy–adhere to this logic. But so do metric wrenches, triple-A batteries, and other devices that rely on universal standards. The more common they are, the more it pays you to stick to that standard. We have an even older example in the English language. Wherever the expense of churning out another copy becomes trivial (and this is happening in more than software), the value of standards and the network booms.
In the future, cotton shirts, bottles of vitamins, chain saws, and the rest of the industrial objects in the world will also obey the law of plentitude as the cost of producing an additional copy of them falls steeply.
PLENTITUDE NOT SCARCITY
Proprietary, or “closed,” systems were once rare…
…because industrial systems were relatively uncomplicated. Proprietary systems rose in popularity as advancing technology made it difficult to replicate a system without assistance or encroaching on patents. The creators of a closed system made a nice living. When the information economy was first launched several decades ago, the dream was to own and operate a proprietary system–one that no one else could copy–and then let the money roll in. To a degree that can still be done, at least for short period, if the system is significantly superior. Bloomberg terminals in Wall Street traders’ offices is one current example. But the network economy rewards the plentitude of open systems more than the scarcity of closed systems. It is a bit of a cliche now to blame Apple’s misfortunes on its insistence that its operating systems be treated as a scarce resource but it’s true. Apple had more than one opportunity to license its particularly wonderful interface–the now familiar desktop and windows design–but backed off each time, thereby guaranteeing its eventual eclipse by the relatively more open DOS and Windows systems.
There is a place for isolation in the infancy of systems, but openness is needed for growth because it taps into a larger wealth. Citibank pioneered the use of 24-hour instant cash at ATMs in the 1970s. They blanketed New York City with their proprietary machines, and at first this strategy was highly successful. Smaller competing banks started their own tiny and proprietary ATM networks, but they couldn’t compete against the high penetration of Citibank machines. Then, led by Chemical Bank, these smaller banks banded together to form an open ATM network called Plus. The power of n2 kicked in. Suddenly any ATM was your ATM. Citibank was invited to join the open Plus network but declined. Following the principle of increasing returns, the handy Plus system attracted more and more customers, and soon overwhelmed the once dominant Citibank. Eventually the open factor forced Citibank to forgo their proprietary ways and join.
PLENTITUDE NOT SCARCITY
Every time a closed system opens…
…it begins to interact more directly with other existing systems, and therefore acquires all the value of those systems.
In the mid 1980s I was associated with a pioneering online community called the Well. You dialed the Well’s special modem, and once logged on you could chat, post, and email anyone you wanted–within the Well. All 2,000 members. Within a short time after start-up the Well made a big jump and opened its mail service to the then-obscure internet. The value of the Well suddenly skyrocketed in the view of its 2,000 or so members because now they could email thousands of academic professors or corporate nerds. A few years later, the Well further opened up its system to a capability called ftp, which allowed Well users to grab files on other internet servers and allowed others to grab files on the Well server. Again, the value of the Well exploded; with only a small effort it gained the tremendous value of the entire ftp network. Eventually the Well opened up even further, allowing users to join the conversation via the web, thereby acquiring all the value of the web.
There was a cost in each step. With every inclusion there was less control of the environment, more noise, more danger of disruption by accident or hacker, and more worry that the business model would collapse. At the same time it was obvious that a totally closed Well would have died.
The idea of plentitude is to create something that has as many systems and standards flowing through it as possible. The more networks a thing touches, the more valuable it becomes.
PLENTITUDE NOT SCARCITY
The value of an invention, company, or technology…
…increases exponentially as the number of systems it participates with increases linearly.
The law of plentitude is not about dominance. The self-interest of ordinary business guarantees that every company in the world will strive to get its product or service into every home, or into every store. Popularity is an ancient goal. But that is not what network plentitude strives for.
PLENTITUDE NOT SCARCITY
The abundance upon which the network economy…
…is built is one of opportunity.
While it is true that every additional email address in the world increases the value of all previous email addresses (that’s the primary effect of plentitude) the increase in value happens because each email address is a node of opportunity, not just an artifact. An email address is more than a way to exchange memos. Because email is rooted in a network, opportunity runs in several directions at once. For instance, once it was realized that mail addresses could be archived easily (opportunity number one), it occurred to someone that they could be collected automatically (opportunity two). They could also be mailed to in bulk (opportunity three). The domain part of the address could be analyzed and used to detect patterns of usage (opportunity four). Addresses in a Rolodex could be updated automatically by the addressee (opportunity five). The address artifact itself could contain more than just a name; it could also hold other facets of interests that the owner was willing to exchange in certain circumstances (opportunity six).
A hammer is part of only a few networks, but a telephone is a part of many. The more networks a product or service can join, the more powerful it becomes.
Contrast this cascading abundance of opportunities with almost any product of the industrial age–say an electric rotary saw, or a color-fast dye, or a maplewood chair. While some of these objects have a few dual uses (the chair could be used as a step stool or to wedge a door open, and the saw motor could be used to drive a drill), they are pretty much limited to their designed intentions. There is no river of opportunities flowing from them. So that even if chairs, dye, and saws were to become universally abundant, their physical plentitude would not change the world much.
PLENTITUDE NOT SCARCITY
The power of the fax effect–
more fax machines increasing the value of all previous machines–does not rely on the proliferation of Panasonic brand fax machines, or of any particular machine. Since many faxes are sent from laptop computers, or from a server somewhere, the power of plenty derives from opportunities rather than lumps of matter.
As opportunities proliferate, unintended uses take off. In the late 1970s, the Shah of Iran exiled his rival, the Ayatollah Khomeini, to Paris. Since the Shah controlled his country’s media he assumed Khomeini would not be able to reach the Iranian people from France to stir up trouble. But sympathetic Iranian clergy exploited an unsuspected technological opportunity: the cassette tape. Every week in Paris Khomeini’s friends recorded his inflammatory speeches on cheap recorders and smuggled copies (easily disguised as music tapes) into Iran, to be multiplied on $200 duplication machines and passed out to every mosque. On Fridays, Khomeini’s sermons were played throughout Iran on boomboxes. The clerics turned the common tape deck into a broadcast network. I’m sure that not a single engineer who developed cassette tape technology ever envisioned it being used for broadcasting. Electronic media, because it is animated by electrons, is highly susceptible to being subverted by new uses.
Recently Sprint, the telecommunications company, pioneered flat cellular phone pricing–you could make all the cell phone calls you want for a fixed monthly fee. Within days of the pricing, the startled marketing experts at Sprint heard reports that people were using the cell phones as baby monitors. Parents would go into baby’s bedroom with a cell phone, dial the kitchen, and then leave the line open. Voilà!
PLENTITUDE NOT SCARCITY
The more interconnected a technology is…
…the more opportunities it spawns for both use and misuse.
Some of the best video games of all time were elegant little programs that ran on early computers such as the Commodore 64. Millions of C-64s were sold during the early 1980s; most of them lie at the bottom of landfills today. Their flealike memories and lack of disk space have been replaced by Powerbooks and Pentiums. The few still working are sold at collector’s prices. But out on the web, filling niches no one could have predicted, are a flock of emulators. You can download a Commodore 64 emulator onto your Powerbook. At the click of a button it will turn your state-of-the-art workstation into a moronic C-64 (or one of 25 other golden oldies) so you can play an ancient version of Moondust, or PacMan. This is equivalent to having a switch on the dashboard of your Ferrari to make it run like a VW Bug.
These refreshing street uses for technology stem from the plentitude of interactions. Artifacts of the industrial economy yield limited potential for such weird, tangential uses. The network economy, on the other hand, is a cornucopia of products and innovations that cry out to be subverted in new ways. Indeed, in a network, new opportunities arise primarily when existing opportunities are seized. A business that successfully occupies a niche immediately creates at least two new niches for other businesses. There is, for example, no end to the number of companies that will find a niche in email; the more wild ideas that are created, the more wild ideas can be created. The arms race between spammers and readers is only in its infancy.
PLENTITUDE NOT SCARCITY
The law of plentitude is most accurately rendered…
thus: In a network, the more opportunities that are taken, the faster new opportunities arise.
Furthermore, the number of new opportunities increases exponentially as existing opportunities are seized. Networks spew fecundity because by connecting everything to everything, they increase the number of potential relationships, and out of relationships come products, services, and intangibles.
A standalone object, no matter how well designed, has limited potential for new weirdness. A connected object, one that is a node in a network that interacts in some way with other nodes, can give birth to a hundred unique relationships that it never could do while unconnected. Out of this tangle of possible links come myriad new niches for innovations and interactions.
PLENTITUDE NOT SCARCITY
A network is a possibility factory.
So tremendous is the fount of plentitude in the network economy that having to deal with nearly infinite choices and mushrooming possibilities may be the limiting factor in the future. Navigating sanely through an expanding ocean of options is already difficult. The typical supermarket in America offers 30,000 to 40,000 products. The average shopper will zoom through the store in 21 minutes, and select out of those 40,000 choices about 18 items. This is an amazing feat of decision making. But it is nothing compared to what happens on the web. There are one million indexed web sites, containing 250 million pages. To be able to find the right page out of that universe is astounding, and the number of pages doubles every year. Dealing with this plentitude is critical because the totals of everything we manufacture in the world are only compounding. The total amount of information stored in the entire world–that’s counting all the libraries, film vaults, and data archives–is estimated to be about 2,000 petabytes. (A petabyte is a billion megabytes, or about a quadrillion books the size of this one.) That’s a lot of bits.